Cyber security
SEAD4 × SRD
Cyber security that evolves through proactive monitoring and R&D for security
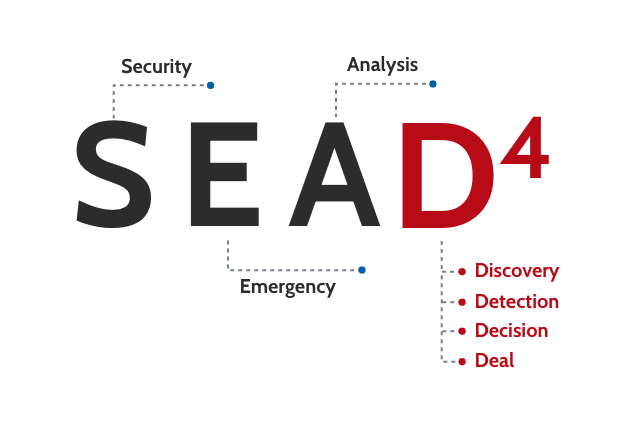
- *SEAD4
- : In-house security operation center (SOC)
- *SRD
- : SOC is an independent R&D team specializing in cyber security.
While the business environment surrounding enterprises is forecast to keep changing significantly, ICT will remain the key to the success of DX and many other important measures.
This implies that the threat of cyberattacks will intensify and cyber defense will become more important.
“K’s-EDR” detects the latest cyberattacks and analyzes their mechanisms and trends, to realize proactive monitoring, which will not overlook the signs of attacks.
As we offer monitoring services globally, we can enhance the cyber security measures of enterprises inside and outside Japan.
*We are offering our services in 14 countries (as of December 2025).
“SEAD4,” which offers a manned monitoring service for security
“SEAD4” is a professional cyber security team with plenty of experience and knowledge. It offers “K’s-EDR,” an end-point manned monitoring service, 24 hours a day, 365 days a year.

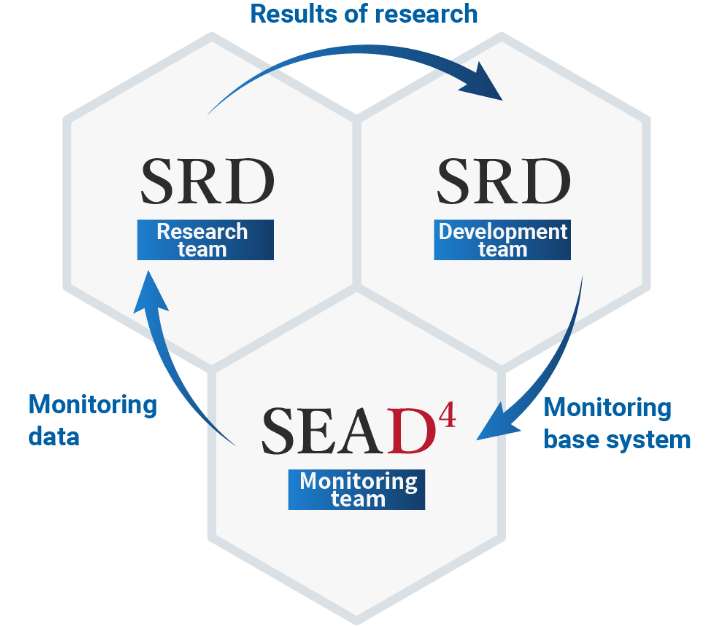
“SEAD4,” an SOC team that conducts monitoring, and “SRD,” a security R&D team, evolve cyber security technologies and offer advanced services. We protect the information assets of our clients from cyberattacks and support their sound business growth.
Strengths of K’s
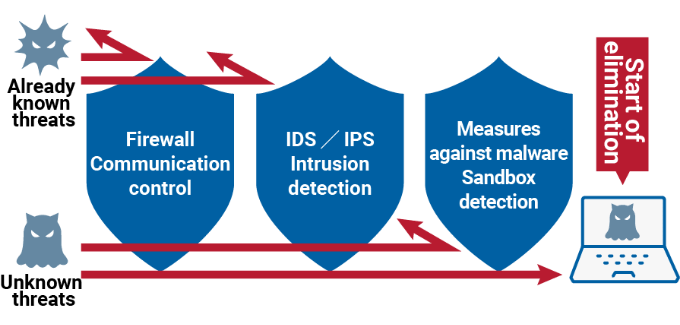
STRENGTH_01Fortification of the security base of each client by the domestic SOC of our company
“SEAD4,” an operation center run by our company, is in charge of “K’s-EDR,” an EDR service that enables the early detection of and swift response to cyberattacks that slip through antivirus software, firewalls, etc. Our security analysts keep a lookout for suspicious programs in clients’ end points, such as servers and PCs, 24 hours a day, 365 days a year, and swiftly take measures for preventing the aggravation of damage if any cyberattack is detected.

STRENGTH_02K’s-EDR service available also at overseas corporations and overseas business sites
We offer a global support for K’s-EDR.
We have a track record of providing MSS service in 14 countries (as of December 2025) and IR (Incident Response) service in some countries. Our cybersecurity team promptly responds to serious security incidents in order to clarify causes, restore operation smoothly and solve issues early.
*MSS: Abbreviation of “Management Security Service” including a monitoring service by SOC

Business sessions with the executives of government ministries and agencies of EU countries and enterprises

STRENGTH_03SRD, a specialized organization that researches and develops technologies for coping with malware
K’s SRD (Security Research & Development) team is a specialized organization that researches and develops technologies for coping with malware and is independent of the SOC team in charge of monitoring. This team researches technologies for blocking cyberattacks of malware, which is becoming more sophisticated and more cunning, and reflects the results of research in the monitoring base system of SEAD4, to evolve cyber security technologies. It supports the advanced monitoring service for detecting cyberattacks early and minimizing damage.

List of services
K’s-EDR
It monitors end points 24 hours a day, 365 days a year, and detects cyberattacks from suspicious programs early. The security analysts of SEAD4 visualize the security risks of attacks and grade threats. If a threat is found, they will swiftly implement stopgap measures at end points, to minimize damage.
Features of K’s-EDR
- In-depth investigation, including correlation analysis of EDR logs and security device logs, to clarify the entire picture of cyberattacks.
- The EDR system is operated and managed by SEAD4, so that there is no burden on clients for operation.
- Since the launch of the EDR service in 2018, there has been no serious incident.

K’s Secure Net
SEAD4 of K’s and “JSOC,” a security monitoring center operated by LAC Co., Ltd., monitor the network environment of each client thoroughly 24 hours a day, 365 days a year. This is a real-time monitoring service which analyzes unauthorized access, which is becoming more cunning, and responds to incidents after detecting intrusion.
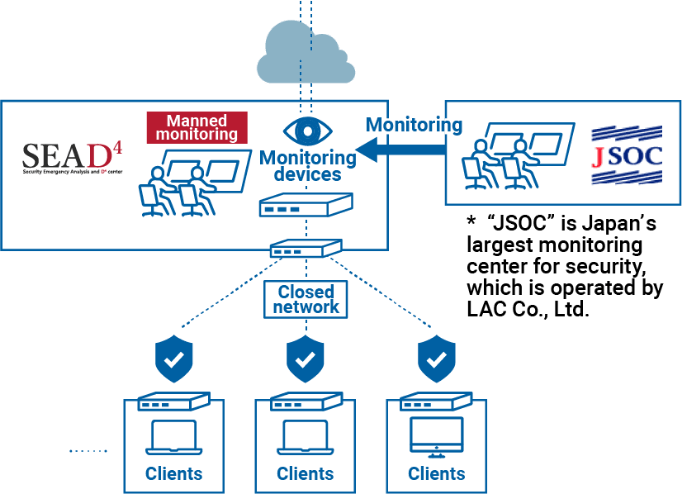
Features of K’s Secure Net
- A broad range of logs can be checked with JSOC, which uses a correlation analysis system and the analysis of security analysts.
- With “JSIG (R),” unique detection rules of LAC Co., Ltd. developed for IDS/IPS, it is possible to deal with domestic threats.

Proper hunting service
We investigate the software used in each company. We check whether vulnerable, risky software is used and grade its threat if it is used. Security analysts of SEAD4 investigate and analyze them, submit the reports on results and hold a reporting session. We improve and enhance security measures for the network environment of each client.

Training service for coping with targeted emails
We conduct training for preventing targeted email attacks disguised as emails from business partners or employees. After the training, we analyze the reasons why spoofed emails were opened and clarify improvement measures. We support the development of an organization with high literacy to prevent damage.

Issues that can be resolved
In order to prepare for increasingly sophisticated and cunning cyberattacks, such as attacks targeting vulnerabilities that cannot be defended against with conventional security measures and targeted attacks, we establish a security monitoring and operation environment leveraging EDR services.
- We want to appropriately respond to security alerts and threats detected from signs.
- We want to outsource the analysis of security alerts and signs.
- We want to detect unauthorized communications, including the spread of malware.
- We want to entrust experts with the difficult task of analyzing an enormous amount of logs.
- We want to build and operate a monitoring system for blocking attacks, including the acquisition and analysis of logs.
- We want to detect threats early, and respond swiftly.
